Why Data Security Is the Top Concern for AI Adoption
As businesses explore AI solutions, data security consistently ranks as the number one concern. This is entirely reasonable. AI systems often need access to sensitive business data, including customer records, financial information, internal communications, and proprietary knowledge, in order to function effectively.
The fear of data leaks, unauthorized access, or non-compliance with regulations has caused many businesses to delay their AI adoption. However, avoiding AI altogether is not a viable long-term strategy. The better approach is to understand the risks and implement AI solutions that are designed with security as a foundational principle.

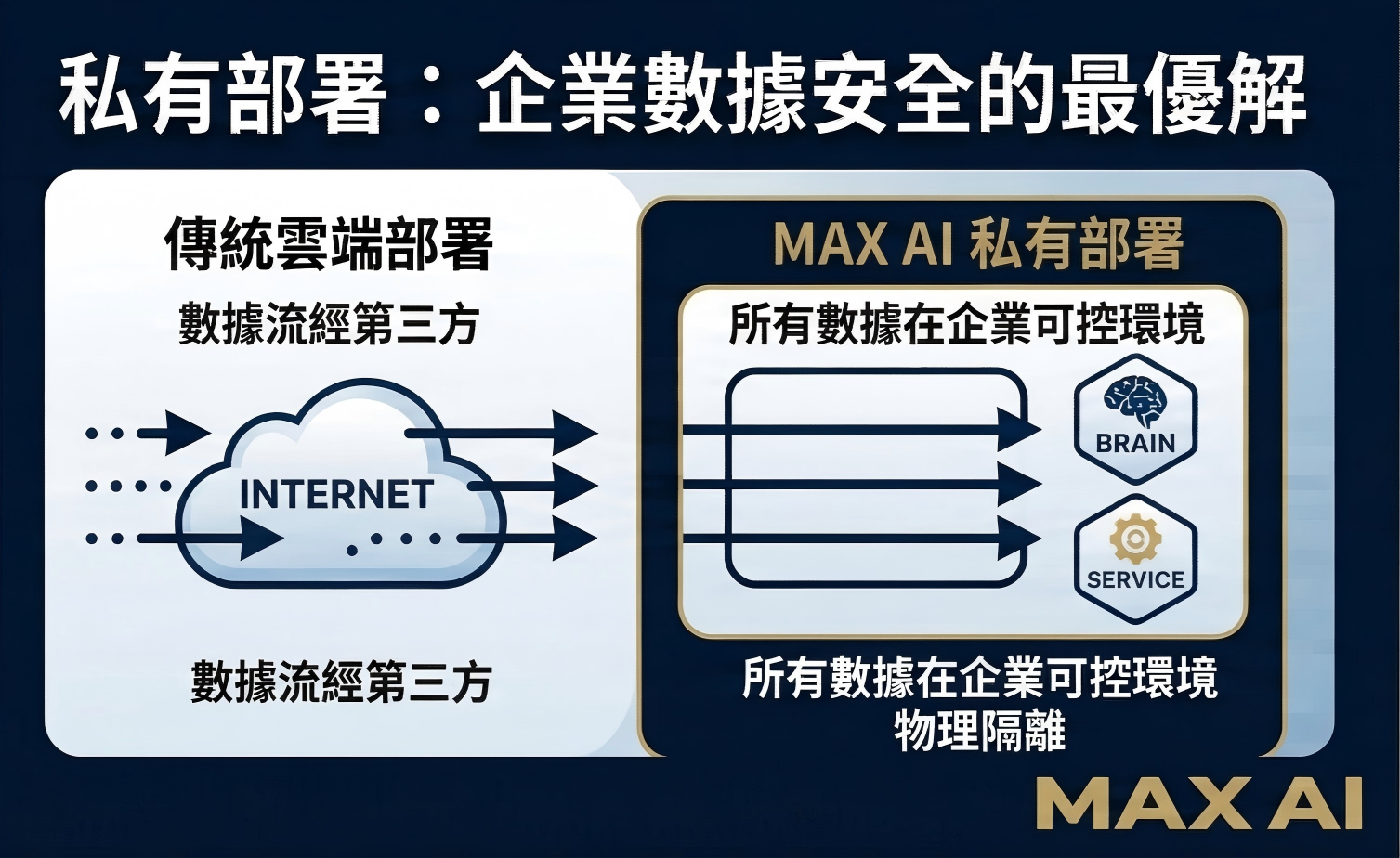
Private Deployment vs. Cloud AI Services
One of the most important architectural decisions in enterprise AI is whether to use cloud-based AI services or deploy AI models on your own private infrastructure. Cloud services offer convenience and lower upfront costs, but they typically require sending your data to third-party servers.
Private deployment keeps all data within your own environment. Your documents, conversations, and knowledge base never leave your servers. For businesses handling sensitive client data, operating in regulated industries, or simply wanting maximum control, private deployment is the preferred choice.
At MAX AI, we specialize in private deployment solutions that give businesses the full power of modern AI while keeping all data securely on premises. This eliminates concerns about third-party data exposure entirely.
Encryption, Access Control, and Audit Trails
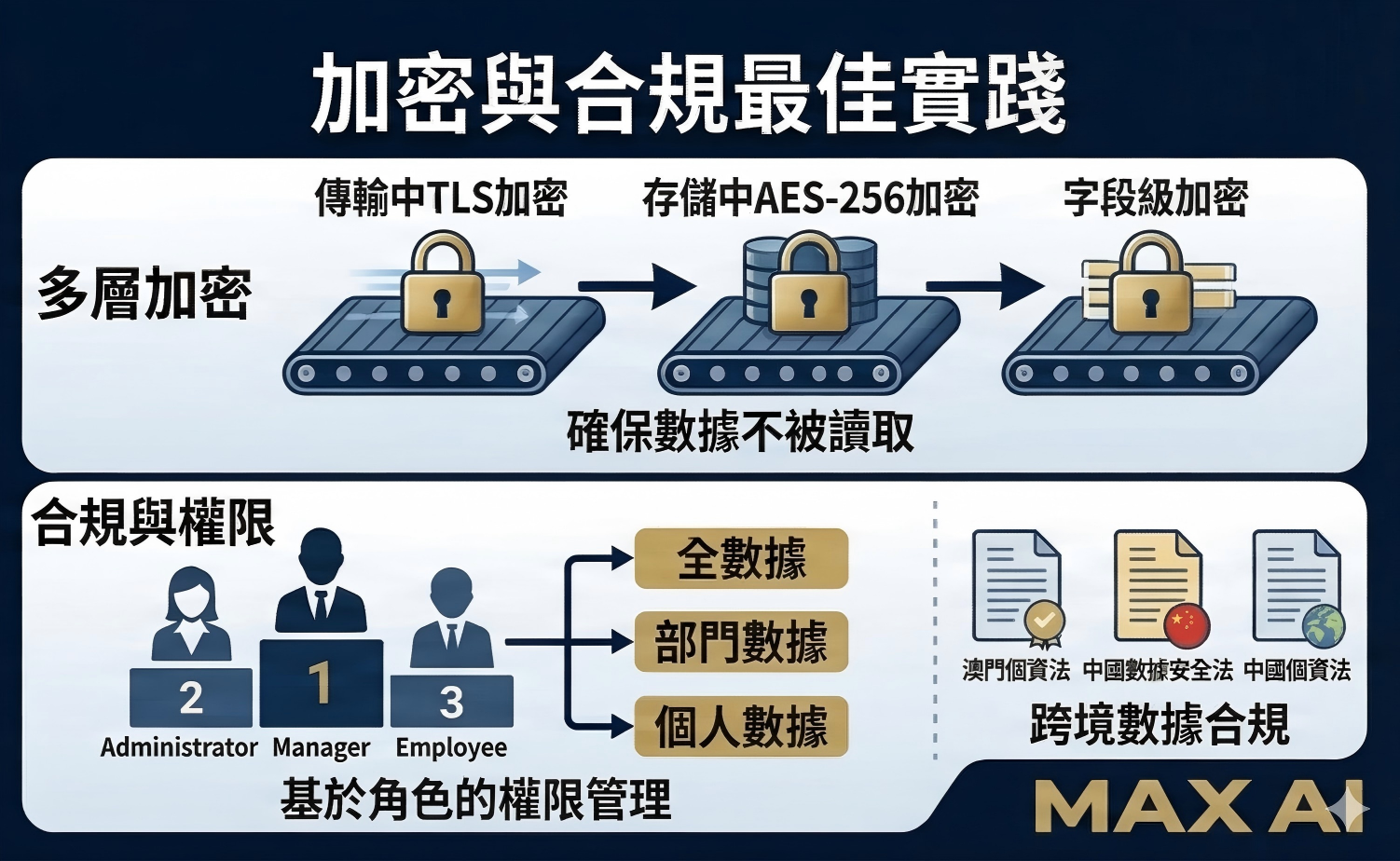
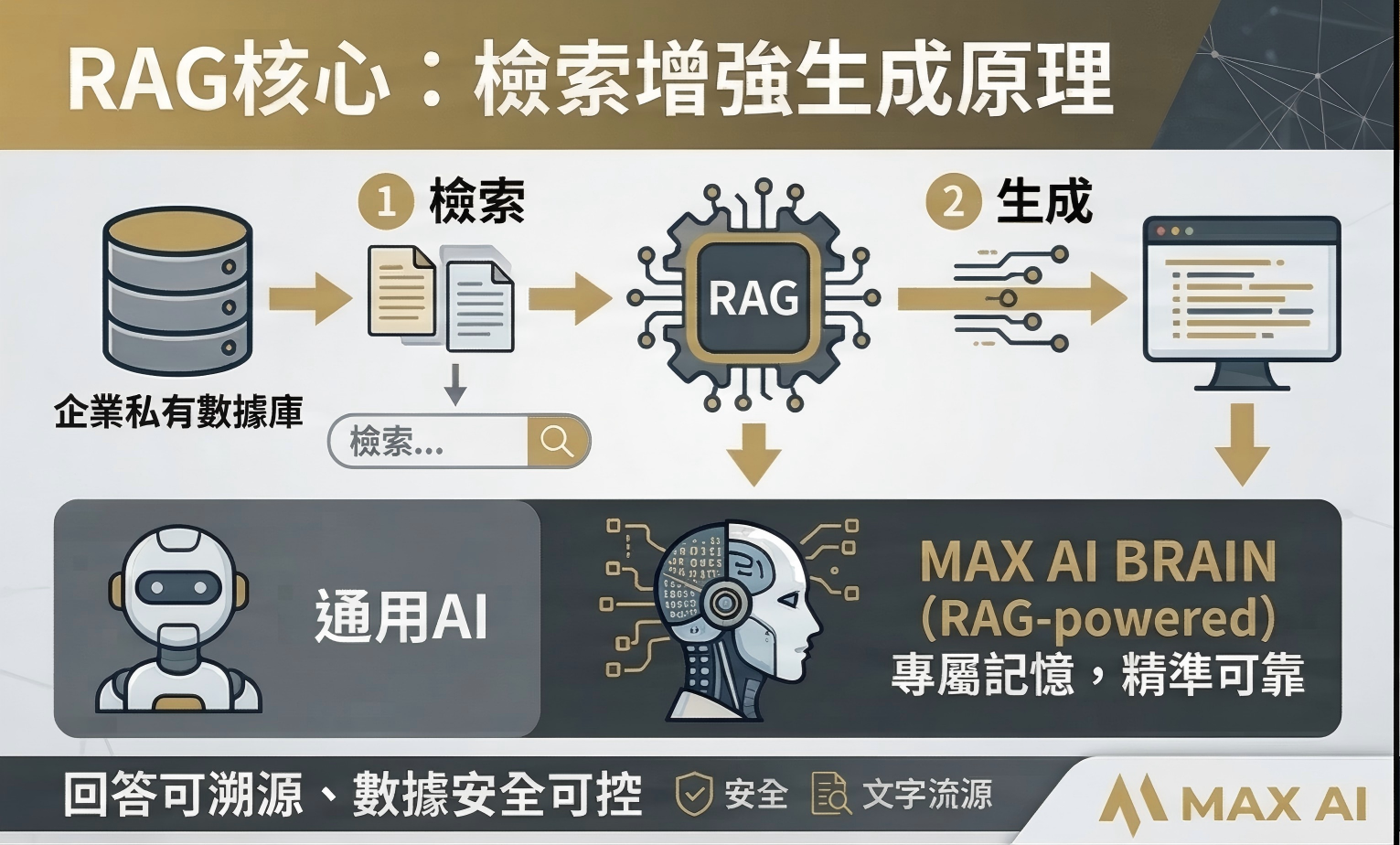
A properly secured AI system implements multiple layers of protection. Data encryption ensures that information is unreadable even if unauthorized access occurs. This applies to data at rest, stored in databases and file systems, as well as data in transit between systems.
Role-based access control ensures that each user can only access the AI capabilities and data relevant to their role. A sales representative should not be able to query the finance team's knowledge base, and vice versa. Comprehensive audit trails record every query, response, and system interaction, enabling full accountability and compliance reporting.
Meeting Compliance Requirements
Businesses operating in Macau and the Greater Bay Area must comply with the Macau Personal Data Protection Act and potentially the mainland China Data Security Law and Personal Information Protection Law, depending on their operations.
A well-designed AI deployment addresses these requirements from the outset. This includes data minimization, ensuring the AI only accesses the data it needs; purpose limitation, restricting data use to defined business functions; and providing mechanisms for data subject rights such as access, correction, and deletion requests. Working with an AI partner that understands these regulatory requirements is essential for a compliant and worry-free deployment.